A Distributed Surveillance System
Xiaojing Yuan and Zehang Sun
Department of Computer Science, UNR
 |
 |
A Distributed Surveillance System Xiaojing Yuan and Zehang Sun
|
|
There has been a growing interest and efforts in
the surveillance industries to build optical sensor based
automatic systems - Intelligent Vision-based Surveillance
Systems(IVSS). IVSS aims to automate object detection,
recognition, tracking and activity understanding in dynamic
scenes. It is of great social importance due to its potential
value to enhance security. IVSS involves many of the core topics
in computer vision area such as moving object detection, tracking,
classification, activity learning and semantic interpretation of
object behaviors.
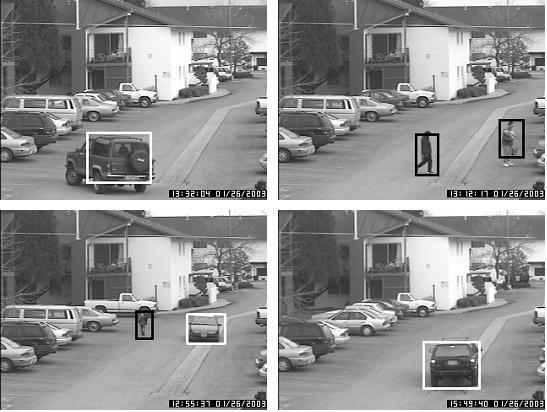
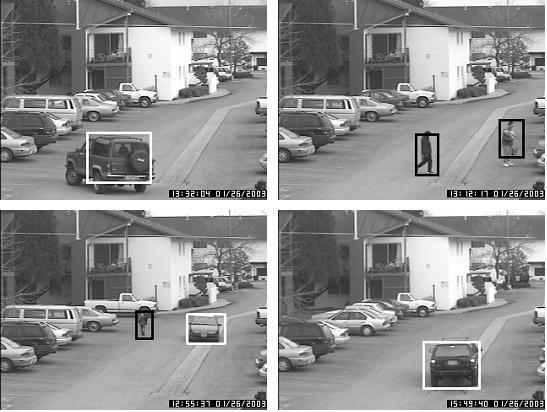
We have developed a trainable distributed surveillance system using static optical sensors. Not just a motion detector, this vision-based system is specifically designed with the capability to recognize certain objects(unauthorized vehicle, people, or animals). It minimizes false alarms due to other non-interested intrusions. When a suspicious intrusion is detected, an alarm indicating the type of the intrusions(vehicle, people etc.), the spot of the intrusions (observation area I, observation area II, etc.) will be sent to the server (customer's security control center) along with the corresponding video display. From application perspective, the main features of this system are: First, it is a trainable system i.e. we can easily train the system for different usages, for instance, alert us when vehicles, pedestrians or pets are present in some observation area. Second, it is a distributed system - heavy computations are distributed to terminal PCs. And it can monitor multiple areas simultaneously and fuse the alert information in the server to make a consensus decision. Technically speaking, the whole system consists of multiple cameras connected by a Local Area Network (LAN), vision-based object detection and classification algorithms. Our vision-based algorithm is a two-stage approach: Hypothesis Generation(HG) and Hypothesis Verification(GV). Specifically, HG hypothesizes the possible threat locations using background subtraction method and HV verifies if there are true threats. HV, essentially, is a pattern classification problem and we use Gabor filter to extract features and Support Vector Machines(SVM) to perform the classifications.
|
|
| Main |
Overview | Methodology | Results
| Future Work | Publications | Acknowledgement |
| UNR-CVL | UNR-Home Page | |